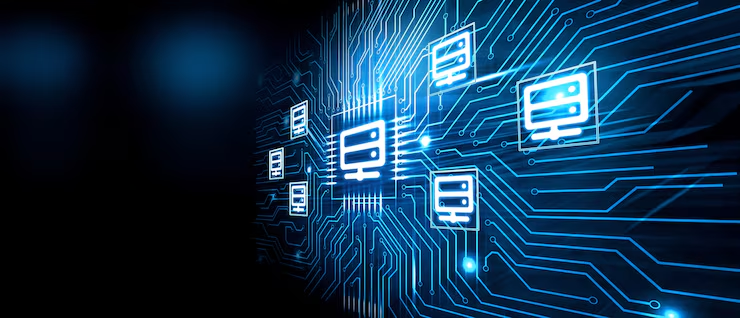
Database access control is a fundamental aspect of modern IT environments, ensuring that only authorized users can interact with sensitive data. As organizations generate and store massive amounts of information, implementing effective database access levels becomes essential for maintaining confidentiality, integrity, and availability. At its core, database access control defines who can access the database, what actions they can perform, and under what conditions those actions are allowed.
Understanding Database Access Levels
Database security access levels are structured hierarchies that determine the degree of access a user has within a system. These levels range from read-only permissions to full administrative control. By assigning appropriate database user roles and permissions, organizations can limit unnecessary exposure to critical data. This structured approach is a key component of access control in database systems, helping reduce risks such as data breaches and unauthorized modifications.
Role of Authentication and Authorization
Two critical components of database access control are authentication and authorization. User authentication systems verify the identity of users attempting to access the database, typically through passwords, multi-factor authentication, or biometric verification. Once authenticated, database permission management takes over, determining what actions the user is allowed to perform.
This process is closely tied to database identity management, where user identities are maintained, monitored, and updated. Together, these mechanisms ensure that only verified users gain access, and only within their permitted scope.
How Access Control Models Work
There are several models used in database access control, with Role-Based Access Control (RBAC) being the most common. RBAC assigns permissions based on roles rather than individual users, simplifying database permission management. Another approach, Attribute-Based Access Control (ABAC), uses attributes such as user location, device, or time of access to make decisions.
These models are essential for building a secure database architecture, as they provide flexibility and scalability while maintaining strict data security and access control standards.
Importance of Data Protection Strategies
Effective data protection strategies rely heavily on well-implemented access control systems. By restricting access through defined database access levels, organizations can prevent unauthorized data exposure and ensure compliance with regulations. Additionally, monitoring and auditing access activities are crucial for identifying suspicious behavior and strengthening database risk management practices.
Conclusion
In today’s data-driven landscape, database access control is not just a technical requirement but a strategic necessity. By combining robust user authentication systems, well-defined database user roles and permissions, and advanced access control models, businesses can create a resilient secure database architecture. Ultimately, effective data security and access control measures safeguard valuable information and support long-term organizational success.